What`s New
On the use of LLM (“AI”) in security decisions
- Albert Zenkoff
- 2026-03-29
- Technology, Artificial Intelligence, LLM, long-term view, perspective, philosophy, security, technology
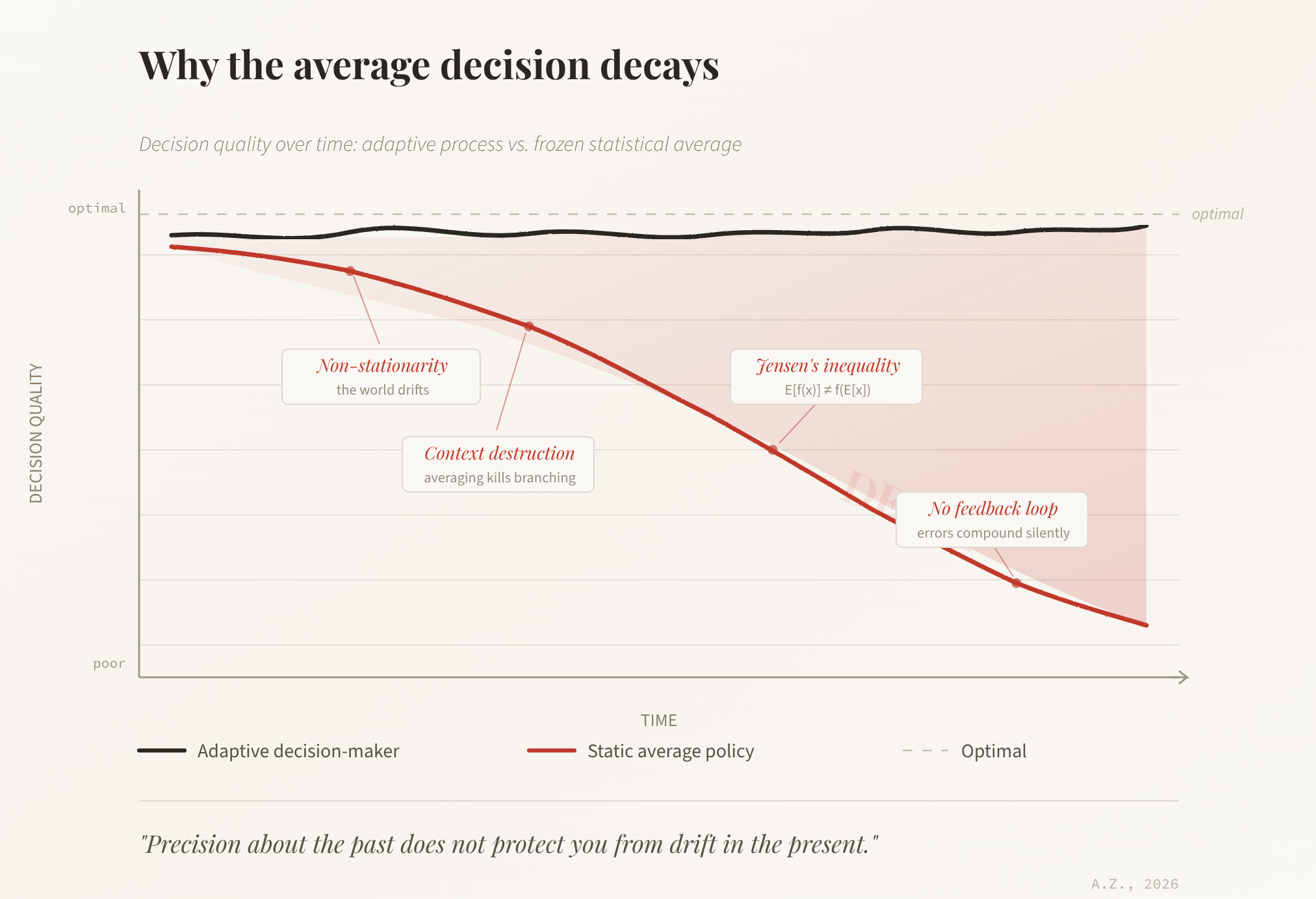
What will happen if we keep using Large Language Models as the basis of decisions, especially in a field like security? Would taking the statistically average decision from this moment on, at every step, lead to a decay of decision correctness over time, or would it stay stable? The question sits at the intersection of ...
Read MoreAI Software Design Security and Language Choice
- Albert Zenkoff
- 2025-11-30
- Technology, Development, technology
Or, rather, the quality of the Artificial Intelligence (AI) generated software in general but it goes for security as well, naturally, since security and quality are but the two sides of the same coin. Software engineers happily embraced the wonderful possibility of being able to program in a natural language – describing the task to ...
Read MoreCAST workshop on development security
- Albert Zenkoff
- 2018-03-13
- General, CAST, cloud, cloud security, conference, DevOps, security, workshop
We are holding our yearly security conference in Darmstadt on the 22nd of March – that’s next week – together with our partners from Fraunhofer SIT and CAST. This time, the focus subject will be DevOps and cloud technologies, including both operations and development preparation for the security in the cloud. The speakers are prepared ...
Read MoreA company with an SQL injection name
- Albert Zenkoff
- 2017-01-19
- Society, attack, company, fun, prank, security, SQL injection
Finally, someone registered a company that is an SQL injection attack. We saw the license plates on cars doctored to execute SQL injection attacks but this is the first time, I think, that an attempt to crash all business SQL databases in a country is made. The company name is: ; DROP TABLE “COMPANIES”;– LTD ...
Read MoreDon’t patch it, it’s fine?
- Albert Zenkoff
- 2016-11-17
- Society, application security, corporate, management, security strategy, society
I wrote back in 2013 about my shock at discovering that the companies are now publicly calling to stop the investment in security and avoid fixing security bugs in my article Brainwashing in security. There, we witnessed the head of Adobe security, Brad Arkin, tell us that the companies should not be wasting their precious ...
Read MoreData breach at LinkedIn
- Albert Zenkoff
- 2016-05-26
- Society, breach, break-in, data breach, database, hack, LinkedIn, passwords, stolen
Apparently, there was a serious data breach at LinkedIn and many customer records were stolen including “member email addresses, hashed passwords, and LinkedIn member IDs”. LinkedIn sent out a notification informing that the passwords were invalidated. What is interesting in the note is that they included a cryptic note that the break-in was “not new”. ...
Read MorePosition yourself on Security Maturity Grid
- Albert Zenkoff
- 2016-02-09
- Management, company posture, cost, grid, improvement, management tool, security management, security maturity, tool
I wrote up the Security Maturity Grid the way quality management is usually presented. The grid is a simple 5 x 6 matrix that shows different stages of maturity of the company’s security management against six different security management categories (management understanding of security, problem handling, cost of security, etc). The lowest stage of maturity ...
Read MoreWorst languages for software security
- Albert Zenkoff
- 2016-01-19
- Technology, C/C++, Development, Java, languages, misleading, OWASP, philosophy, problem, quality, security promise, vulnerability, web application
I was sent an article about program languages that generate most security bugs in software today. The article seemed to refer to a report by Veracode, a company I know well, to discuss what software security problems are out there in applications written in different languages. That is an excellent question and a very interesting ...
Read MoreBackdoors in encryption products
- Albert Zenkoff
- 2015-12-15
- Society, backdoor, crime, encryption, illegal, legal, prediction, problem, surveillance, unauthorized
After the recent terrorist attacks the governments are again pushing for more surveillance and the old debate on the necessity of the backdoors in encryption software raises its ugly head again. Leaving the surveillance question aside, let’s see, what does it mean to introduce backdoors to programs and how they can be harmful, especially when ...
Read MoreCAST Workshop “Secure Software Development”
- Albert Zenkoff
- 2015-09-21
- Management, best practices, CAST, event, security, share, software development, workshop
We are organizing the workshop on “Secure Software Development” now for the third year in a row. As usual, the workshop is in Darmstadt and the logistics is cared for by the CAST e.V. The date for the workshop is 12 November. This year most presentations seem to be in German, so probably it does ...
Read More